
The Chief Intelligence Strategist for ‘Treadstone 71’ Jeff Bardin presents his overview of cybercrime from several different angles. Mr. Bardin describes cyber fraud as viewed from within this industry, outlining such aspects as credit card fraud, botnet operations, spam distribution, phishing, money mule recruiting schemes and software vulnerabilities exploited by the criminals. Importantly, you will also get to learn how these activities relate to international terrorism.
My name is Jeff Bardin, and we will talk about malware. We are also going to speak on malware’s ties to terrorism, as well as card and ID markets, and these card and ID markets were pretty impressive. And we will talk a little bit about the FBI’s hands into these markets and what they did to take them down.
So let’s get into the malware right away here, we will talk to that. So, most people know about zero-day malware attacks. This is when there is a vulnerability that is undiscovered in software, usually on the Internet or even on your desktop. It’s undiscovered by the software company or the authorities, let’s put it that way. What it is discovered by is the cyber criminals because they will go out and continually reverse-engineer and search for vulnerabilities in software. They are constantly scanning, probing, searching for these vulnerabilities, and they find them before companies know they are there, and before they can actually create a fix for that software.
A zero-day attack or threat is a computer threat that tries to exploit computer application vulnerabilities that are unknown to others or the software developer. Zero-day exploits (actual software that uses a security hole to carry out an attack) are used or shared by attackers before the developer of the target software knows about the vulnerability.
Wikipedia
So zero-day is something that they exploit on a regular basis. We have seen it most recently with Stuxnet1. But it is a constant battle and their whole ‘modus operandi’ is to find these and then incorporate into their malware products.
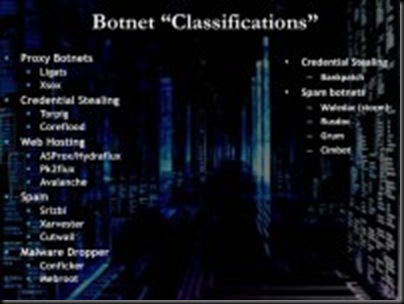
Botnet classifications
So there are a lot of different botnet2classifications here. As you see on the image, there are proxy botnets that you can use to secure information and stop people from tracking you. There’s credential stealing, using trojans and other information; web hosting sites that actually look and smell just like banking sites, but in fact they’re not – they look exactly the same, but when you go to those sites you can be immediately affected with a zero-day malware attack. There’s spam out there as well, where people will click on links that take them to sites that actually will download software, and you won’t even know that you’re infected, it does it very quickly and effectively. There’s malware droppers, and the credential stealing we talked about in the spam botnets out there.
So, when you become infected with a botnet, something that will give you an indication that you’re infected is the constant flashing of the lights on your machine because it’s overworking and you are actually now a zombie in the botnet – you are part of it and you have been infected.

Rack environment run by cybercriminals
So let’s continue on here. This is a picture here of maybe a rack environment at a hosted data center. If you follow the words on the image, this is basically how they set up their infrastructure: spam content servers, pharmaceutical fraud sites where people will go and buy and sell Viagra and different information, so you may get the Viagra, sometimes you’ll get bogus drugs, but what they are really after is your credit card information.
Money mule3 sites that will go out there and offer jobs in the downmarket – these sites will offer lots of jobs out there, but when go into the jobs section of this website – it looks very legitimate – only one job will be open, and that’s the money mule job, where they’ll transfer money into your account so that you basically launder it, or they’ll send goods to your house that you’re supposed to store and forward, and eventually you’ll get caught because you are just a mule. That lasts usually from one month to three months before you get nailed unsuspectingly, but in the downmarket that’s done frequently.
Malware drop sites, the infection sites, rogue name servers out there, child pornography sites, phishing are there as well.
Rogue payment processing sites look exactly like payment processing sites for credit cards when in fact they are completely bogus and they are stealing your information as you enter it. Bank account intrusion sites, distributed denial-of-service sites are out there, and the carding forum sites where credit cards are bought and sold.
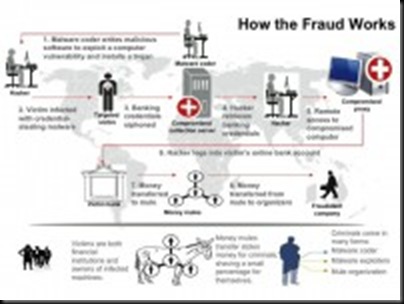
Cyber fraud functioning scheme
This is a part of the infrastructure out there, and I am going to talk a little bit too here on how the fraud actually works (see image). So, a malware coder goes out and writes the code for a zero-day attack along with bundling it up with multiple payloads, meaning – put a trojan in there, the trojan will install on your machine, and then it can send information out through a secure channel.
Once it exploits a vulnerability in the software on your machine, it drops the software onto your machine. Then, as you go into your bank site from your PC, it keystroke logs your user ID, password information, and then gets into the bank site and steals information there. It will save that information onto your machine, and then through that trojan and this secure HTTPS connection it’ll send that information back to a collector site, where it stores it and eventually moves it back through possibly the other site. And this jumps around the world until it eventually gets back to the cybercrime organization.
Now, that’s one model of this. Other models are such that you can actually buy the software, and they have become a software house where you can buy the Zeus software (most people know about it), set it up on your own servers, and you can become the purveyor of the cybercrime software. And the people that write this software then will send out updates to you. They will send out software updates and push it to you with the service-level agreement that you have paid for when you bought this software.
So it has become quite an industry out there. And this is one example here of the money mule activities, where once, say, they do get that information, they may create credit cards from it, give it to a mule who then will go out to a bank site or go shopping, buying high-end goods such as Gucci handbags or whatever. They take that material and will post it on the eBay site, sell it for less than the normal price out there to move it quickly, take that money and then pay off the mules, but with a small amount, and refund their whole process.
So this is just a couple of the models out there that are being used today, and they are very effective, efficient and they continue to evolve and avoid our defenses.

Tariq al-Daour, Younis Tsouli and Waseem Mughal
So, what are some of the ties to terrorism here? How does terrorism fit into the cybercrime market? We’re gonna touch on that right now. Back in 2003, these three gentlemen here (left to right on the image): Tariq al-Daour, Younis Tsouli and Waseem Mughal – indulged in terrorist activities. Now, the one that’s most well-known is Younis Tsouli, or better known as Irhabi 007, or Terrorist 007. But he was not actually the brains behind it, it was actually Tariq, the gentleman on the far left.
So they used a lot of information out there that they would send back at the time to Iraq, and gentleman al-Zarqawi eventually was removed from the Earth by a couple of five-hundred-pound bombs. Anyway, they would use lot of their fundings here, their collection from illegal activities online to fund terrorist activities in Iraq, until they were caught.
Younis Tsouli came to London with his father from North Africa, attended Westminster College and started taking computer classes to learn a lot about computers. He was basically the computer mind behind this where he would set up a lot of different sites, take videos, compress them, distribute them.
So how did these folks actually fund their operations, where did they come into play with us?
Well, before we get to that, some of the things that Younis Tsouli did here is he would go out and preach Jihad4 on the Internet – communication mechanism, recruiting effort to get other Muslims to come to the aid of the folks in Iraq, funding them: “We want you to develop hacking skills. We want you to be able to steal credit cards out there. We want you to learn how to do this online”.
So, going through these classes himself, he was actually offering courses online on how to do this stuff: how to make bombs, how to learn how to hack. These were all documents, sometimes even videos on how to do this. And he was pushing that across on his cyber Jihadist sites.
And also, trying to get them to do the same, he was saying: “This is Halal5, it’s not Haraam6, it’s good to do this because it’s against the infidel, it’s not forbidden, or Haraam. Because it is in fact against the infidel, so it is okay to do this. And it’s a means to an end. And if you do this you’ll make a lot more money. Of course we want you to contribute that money back to us so we can help fund the cause”. So trying to talk people into this wasn’t very hard, there was a lot of affinity to this with the U.S. Forces being in Iraq.

CBS News report on Madrid train bombing
Quickly back here to Madrid in 2004, this was during the train bombing where nearly 200 people were killed, where simultaneous bombs went off across different train stations, killing 200 different people. This was covered extensively by CBS News (see image). They used Mitsubishi Trium Mobile phones to actually trigger the bombs, they had them in backpacks. But to get these phones, they had to have funding for it.
They traded hashish to a former miner to actually get the explosives. And then, once they got the explosives, they learned how to construct the bombs. And they did that by going to sites, a lot of them propped up by Younis Tsouli and company that had already put them there before. That was starting to get flooded from people connecting out of Iraq, saying: “This how you create an IED7, this is how you create the best bomb, this is how you create the triggers with these particular phones” – video, how-to, specifically showing how you manipulate these and the triggers.
In addition, they found all kinds of drugs on site and they had again to have funding to get these drugs.
And then 2 million dollars in cash and drugs out there were found when these folks were eventually arrested, but it was too late, they had already perpetrated their crime, and 200 people paid for it with their lives.
Then they moved to England in 2007, this was July 2007 when the bombs went off in the subway systems and on the double-decker buses in London. When these folks were actually caught, they found all kinds of credit cards on them as well. They were using these credit cards to actually buy material and then send it out to Afghanistan or Iraq, depending upon their persuasion. Most of this actually went to Afghanistan.
Read next: The machinery of cybercrime 2: terror funding via the Internet
1 – Stuxnet is a computer worm discovered in June 2010. It initially spreads via Microsoft Windows, and targets Siemens industrial software and equipment.
2 – Botnet is a collection of compromised computers, each of which is known as a ‘bot’, connected to the Internet and used for cybercrime purposes.
3 – Money mule is a person who transfers stolen money or merchandise from one country to another, either in person, through a courier service, or electronically.
4 – Jihad is a holy war waged on behalf of Islam as a religious duty of Muslims.
5 – Halal (Arabic: “lawful”) is a term designating any object or an action which is permissible to use or engage in, according to Islamic law.
6 – Haraam (Arabic: “forbidden”) is a term used to refer to anything that is prohibited by the word of Allah (God) in the Qur’an.
7 – IED (improvised explosive device, also known as a roadside bomb) is a homemade bomb constructed and deployed in ways other than in conventional military action.
Read more
http://privacy-pc.com/articles/the-machinery-of-cybercrime-malware-infrastructure-and-ties-to-terrorism.html
